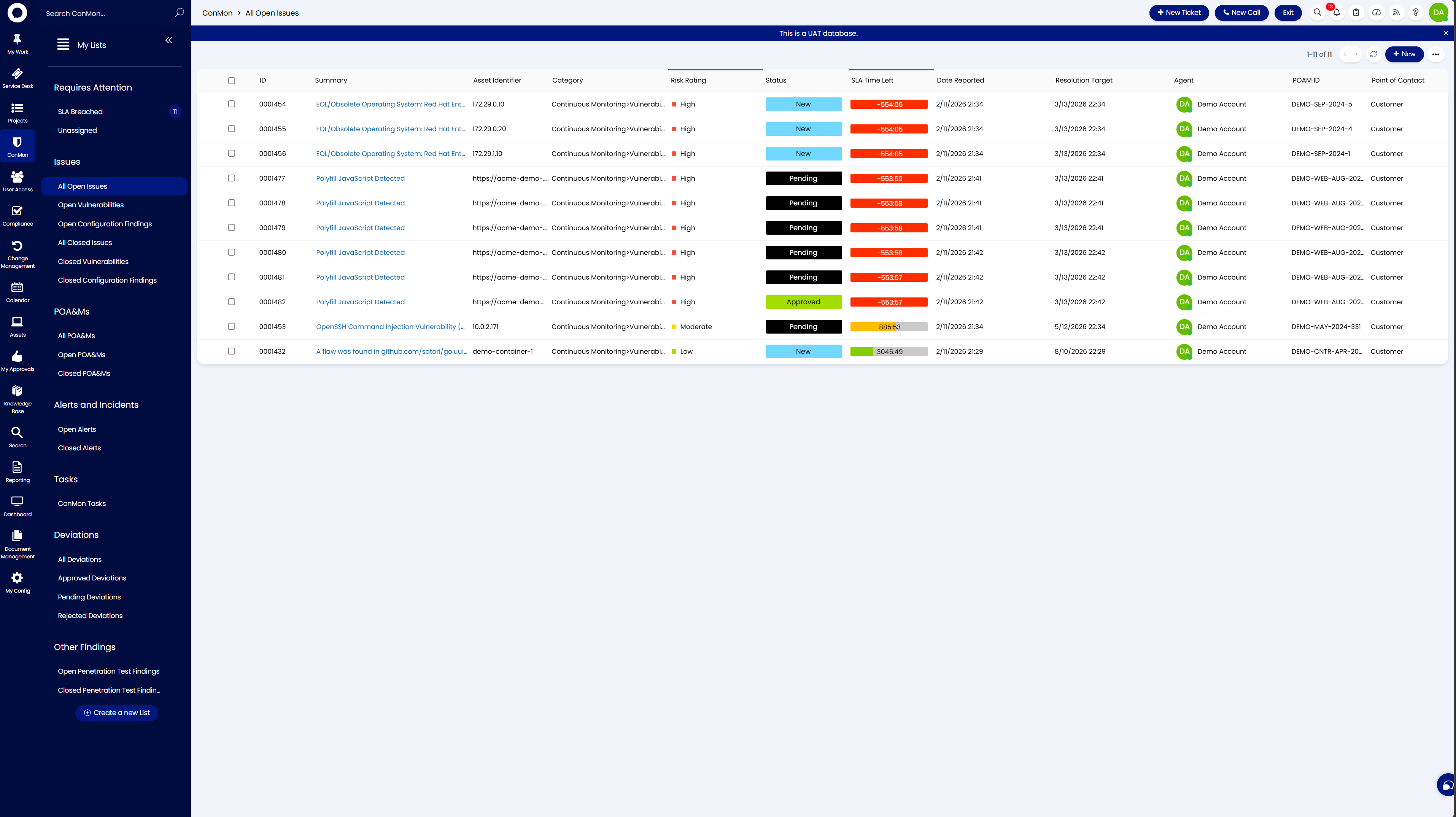
Continuous Monitoring¶
The Continuous Monitoring (ConMon) area is the central working space for security operations across the platform. This is where agents manage the full lifecycle of security findings, vulnerabilities, alerts, incidents, and monitoring activities, from initial discovery through remediation or deviation.
Requires Attention¶
- SLA Breached - findings that have exceeded their remediation SLA targets
- Past Due - findings past their target remediation date
- Due Soon - findings approaching their target date within the next 7 days
Issues¶
The core of ConMon work. Issues represent identified vulnerabilities and configuration findings that need to be tracked and remediated.
- All Open Issues - all active vulnerabilities and configuration findings currently being tracked
- Open Vulnerability Findings - vulnerability scan results requiring remediation
- Open Configuration Findings - configuration baseline deviations requiring correction
- All Closed Issues - all resolved vulnerabilities and configuration findings for audit reference
- Closed Vulnerabilities - resolved vulnerability findings
- Closed Configuration Findings - resolved configuration findings
POA&Ms¶
Plans of Action and Milestones for findings that cannot be immediately remediated.
- Open POA&Ms - active POA&M items with scheduled remediation milestones
- Closed POA&Ms - completed POA&M items
Alerts and Incidents¶
Security events and operational alerts that require investigation or response.
- Open Alerts - alerts from ITDR (Identity Threat Detection and Response) / EDR (Endpoint Detection and Response) systems, workflow errors, or other automated monitoring
- Phishing Alerts - reported phishing emails under investigation
- Tickets - general incident tickets
- Closed Tickets - resolved incident tickets
Deviations¶
Items where a finding has been reviewed and a deviation from standard remediation has been requested. Deviation requests follow the same approval workflow as change requests (CRs) and user access requests (UARs). By default, this is a two-stage process: the internal CAB reviews and approves first, then the request is forwarded to the designated end user with the Deviation Approver role for final sign-off. Approval processes are customizable to suit your organization's needs.
- All Deviations - all active deviation records
- Acknowledged - deviations that have been formally acknowledged
- Pending Deviations - deviations awaiting review and approval
- Accepted Deviations - approved deviations such as false positives and risk adjustments
Other Findings¶
- Open Penetration Test Findings - active findings from penetration testing engagements
- Closed Penetration Test Findings - resolved penetration test findings